This article is divided into below three parts.
- Azure DevOps – Access Restriction of Azure App Service using Azure Management Portal – We will learn how to restrict the access to the Azure App Service manually using the Azure Portal.
- Azure DevOps – Bulk IP Address Restriction of Azure App Service dynamically using PowerShell – We learn how to leverage PowerShell scripting to dynamically do bulk insertion of IP Addresses for configuring access restrictions for the Azure App Service.
- Azure DevOps – Automate Bulk IP Address Restriction of Azure App Service dynamically using PowerShell & Azure DevOps Pipeline We will learn how to automate the process of Access Restriction every time there is a change in the list of IP addresses using Azure DevOps Pipelines.
Prerequisites:
- Azure Subscription
- Azure App Service
Introduction
Azure App Service is a PaaS offering from Microsoft Azure where we can host web applications. Once the web applications are deployed anyone can access the app over internet.
Below are some scenario where you might want to restrict the access of the App Service.
- Your application is an internal application hosted in Azure App Service and you would like to restrict the access only with your Organization IP Address or Network.
- You application is not yet live and you want to allow access ONLY your internal team within a range of IP Addresses till your app goes live.
- You are using Deployment Slots and you don’t want to allow outside people to access the staging slots.
- You are getting automated scraping requests from a set of IP Addresses and you would like to block them.
- You would like to block internet access but you would like to Allow only azure services like Azure Application Gateway or Azure Front Service
- Your app is an API which is NOT meant to be access by public users by only consumed by trusted parties.
In this article, we will learn how to restrict or allow access to the Azure App Service using the Azure Management Portal.
Azure Management Portal
Let’s start by navigating to the App Service (or a Staging Slot) and click on Configure Access Restrictions link which is available in the Networking Blade as shown below.

You will be taken to the Access Restrictions blade as shown below.

Below are the components of the Access Restrictions blade highlighted in the above screenshot.
- The first tab shows all the access restrictions applied the Azure app service.
- The Second tab shows all the access restrictions that are applied for the Kudu website. You can learn more about Kudu at https://praveenkumarsreeram.com/2016/11/23/azure-app-service-and-kudu-the-deployment-framework/ .
- Add Rule button can be used create a new rule to be applied for the access restrictions of the app service.
- And finally you can view all the existing access restrictions that are available for the current app service.
Let’s now add new access restriction rule on the app service by clicking on the Add Rule button.
In the Add Access Restriction blade, you can provide the following values to create a new Allow/Deny rule.
| Parameter | Description |
| Name | The name of the rule. |
| Action | Allow – selecting this option will let the user access the App Service from the given IP Address (in the IP Address Block) Deny – selecting this option will NOT let the user access the App Service from the given IP Address (in the IP Address Block) |
| Priority | The priority given for this rule. |
| Type | Select IPV4 (more on this below) |
| IP Address Block | Provide the IP Address Range. If you would like to mention only one IP Address then provide something in this format 1.1.1.1/32 |
Note: This article focuses on the type IPV4. The process for IPv6 is also same. However, the Access Restrictions feature allows us to control the access using the below types.

You can leave the rest of the fields as they are not mandatory and click on the Add Rule button to add the rule. Once the rule is added. You notice the below two changes.
- The new rule with the values that you have provided will be added.
- The existing Allow All rule with Priority 1 will be changed into Deny Rule with a priority 2147483647
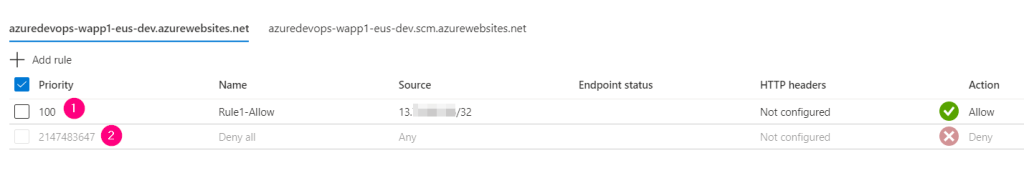
Once you add a new rule (either Allow or Deny) a Deny All rule (shown in the above screen) will be created and no one will be allowed to access the rule except the Allow rules ones which are allowed explicitly using the Access Restriction blade.
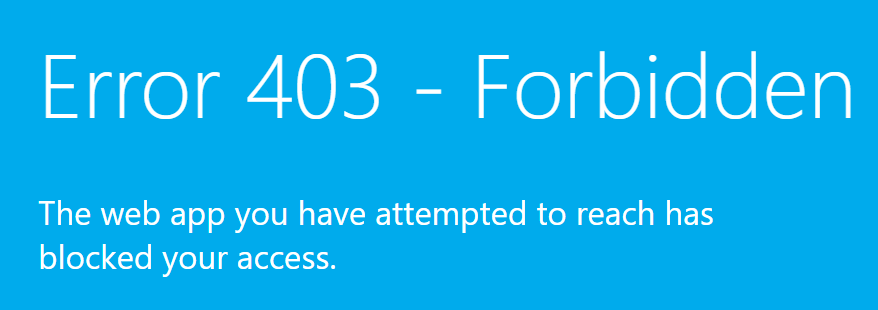
That’s it. We have added an Allow rule for a Single IP Address to access the Azure App Service. Users from other IP Addresses will not be able to access the Azure App Service. If they try to access then they would receive an error with the message “Error 403 Forbidden – The web app your have attempted to reach has blocked your access” as shown below.
In this article, we have learnt how to manually allow/deny the access to a single IP Address using the Azure Management Portal. In the next article, we will learn how to perform Bulk insertion of the IP Addresses using PowerShell.
Hope it helps. Happy learning.
Do you like this article? If you want to get more updates about these kind of articles, you can join my Learning Groups
it was really good to have azure online training with certification
LikeLike