This article is divided into below three parts.
- Azure DevOps – Access Restriction of Azure App Service using Azure Management Portal – We will learn how to restrict the access to the Azure App Service manually using the Azure Portal.
- This article – Azure DevOps – Bulk IP Address Restriction of Azure App Service dynamically using PowerShell– We learn how to leverage PowerShell scripting to dynamically do bulk insertion of IP Addresses for configuring access restrictions for the Azure App Service.
- Azure DevOps – Automate Bulk IP Address Restriction of Azure App Service dynamically using PowerShell & Azure DevOps Pipeline We will learn how to automate the process of Access Restriction every time there is a change in the list of IP addresses using Azure DevOps Pipelines.

Prerequisites:
- Azure Subscription
- Azure DevOps Account
- Azure App Service
Please ensure that an App Service is created.
Introduction
In the previous articles Azure DevOps – Access Restriction of Azure App Service using Azure Management Portalwe have learnt how to manually add an Allow or Deny rule using the Azure Management Portal in the Networking / Access Restrictions blade by providing the below information.
And, we have also learnt how to do a Azure DevOps – Bulk IP Address Restriction of Azure App Service dynamically using PowerShell.
It doesn’t make sense to run the PowerShell script manually every time there are new IP Addresses that needs to be added.
So, in this article, we are going to learn how to automatically execute the PowerShell script from Azure DevOps pipeline.
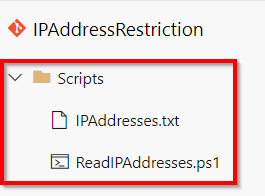
Let’s add both the below files to a Repository as shown below
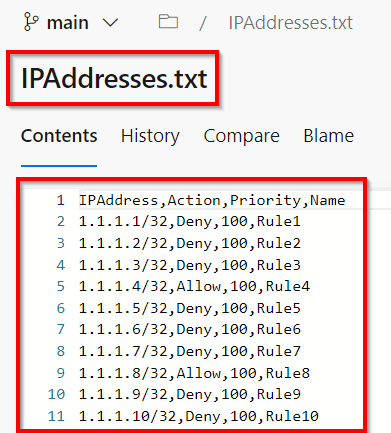
Below is how the IPAddresses.txt files look with dummy IP Addresses.
Let’s understand the next steps.
Build Pipeline: In the build pipeline, we will only be adding the PowerShell script file (ReadIPAddresses.ps1) and the IP Address file (IPAddresses.txt) into the package.
Release Pipeline: In the Release pipeline, we will run the PowerShell script which adds the IP Address restrictions to the App Service – Web App.
Let’s start working on the pipelines.
Package the files using Build Pipeline:
Packaging the files in again a 2-step process.
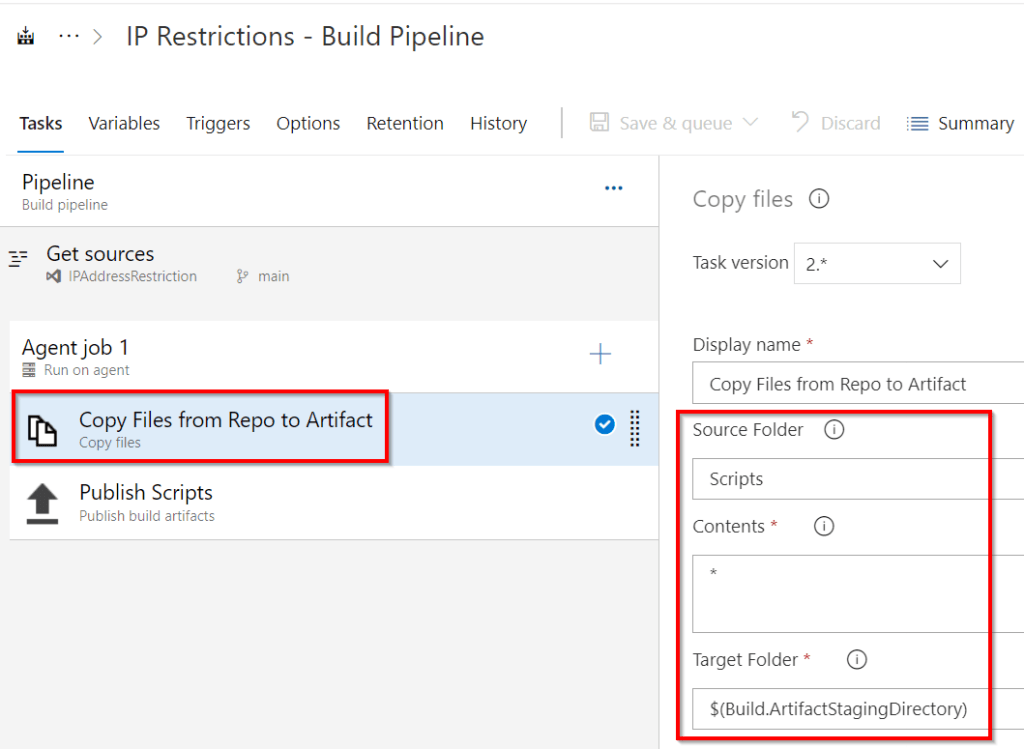
Step1: Download the files from the git repository to the agent – As shown in the below screenshot, this step copies all the contents ( * means all files) from the folder names Scripts into a pre-defined location specified in the Build.ArtifactStagingDirectory location within the agent.
Step2: Publish the Artifactory into the Azure Pipeline – as shown in the below screenshot, this step will publish (upload) the artifacts from Build.ArtifactStagingDirectory location to Azure Pipelines.

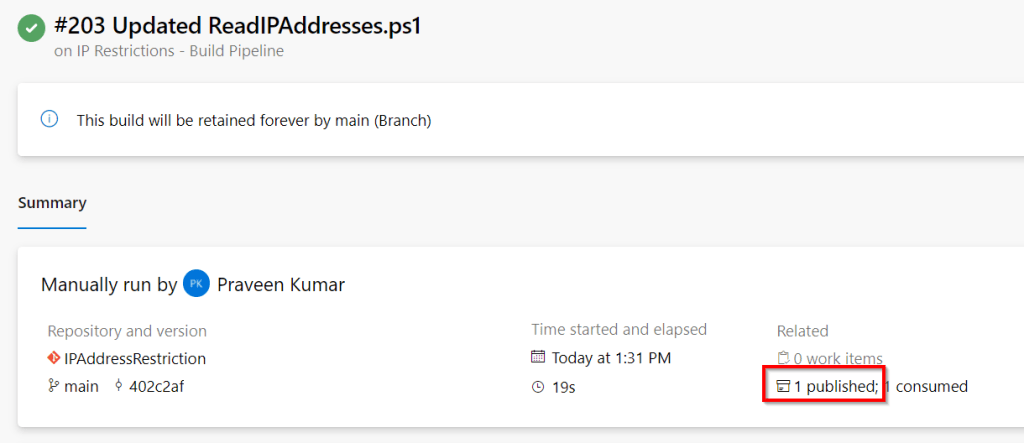
Go ahead and run the pipeline. You should see the below
In the Build Pipeline execution summary screen, click on the Artifacts link to view the published artifacts.
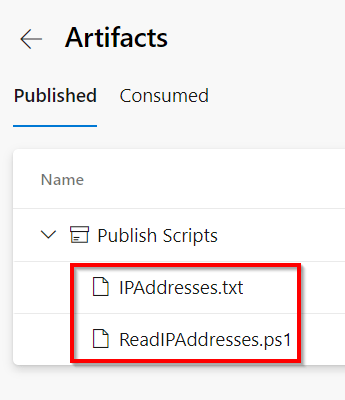
You will be taken to the below screen where you can see the files packaged.
The above screenshots prove that the build pipeline is successful.
Execute the PowerShell with Release Pipeline
In this section, we will learn how to execute the PowerShell script. Let’s create a release pipeline and add an Azure PowerShell task as shown below.

- Choose the file which contains the PowerShell script
- Provide the arguments to the PowerShell Script.
- Resource Group Name
- App Service Web App name
- Location of the file which contains the IP Address list
- Make sure to choose if you are using PowerShell core.
Finally, after you run the pipeline, all the IP Addresses will be added to the Access Restrictions blade as shown below.

That’s it. We have learnt how to add the rules using the PowerShell by integrating it with Azure DevOps pipelines.
Do you like this article? If you want to get more updates about these kind of articles, you can join my Learning Groups
2 comments